Executive Summary
EclecticIQ analysts have conducted in-depth research on ransomware operations, focusing on attacks targeting cloud infrastructures within the insurance and financial sectors. Based on the analysis, the infrastructure and methodologies observed—particularly the automated generation of phishing pages—strongly align with the SCATTERED SPIDER activity cluster [1].
SCATTERED SPIDER frequently uses phone-based social engineering techniques like voice phishing (vishing) and text message phishing (smishing) to deceive and manipulate targets, mainly targeting IT service desks and identity administrators. The actor often impersonates employees to gain trust and access, manipulate MFA settings, and direct victims to fake login portals.
Members of SCATTERED SPIDER likely purchase stolen credentials, executes SIM swaps and use cloud-native tools to maintain persistent access. Analysts have observed that threat actors are leveraging legitimate features of cloud infrastructure to carry out malicious attacks, making their operations increasingly difficult to detect and counter.
SCATTERED SPIDER demonstrates a deep understanding of Western business practices by its predominantly English-speaking members. EclecticIQ analysts assess with medium confidence that this cultural familiarity is one of the critical reasons BlackCat/ALPHV [2] has partnered with them. This partnership has improved the BlackCat Ransomware group’s capability to target Western organisations more effectively.
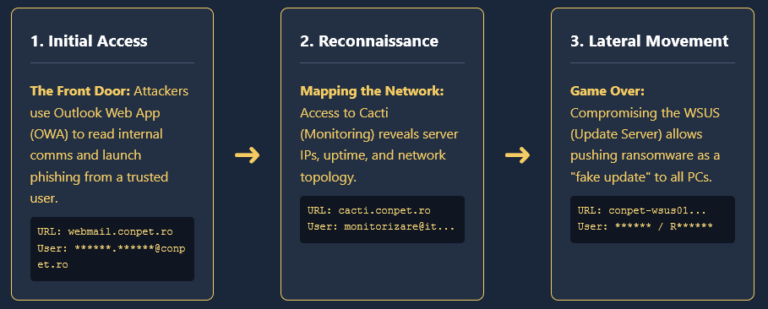
EclecticIQ has developed a Ransomware Deployment Life Cycle to help defenders by detailing the techniques used by the threat actor to infiltrate, persist, and execute ransomware within cloud environments. The cloud’s accessibility, while beneficial to businesses, presents opportunities for financially motivated cyber criminals, making it a prime target.

Figure 1 – Ransomware deployment life cycle
in cloud environments
(click on image to enlarge).
From User Accounts to Cloud Infrastructures
Between 2023 and Q2 of 2024, EclecticIQ analysts monitored and analysed cyber-attacks targeting identity administrators in cloud infrastructures. The findings indicate that SCATTERED SPIDER frequently compromises corporate networks through social engineering tactics against cloud user accounts. The following sections detail the various methods and tools used in these in-the-wild attacks.
Accidental Cloud Authentication Token Leakage
Accidental credential leakage remains a prevalent method for gaining unauthorised access to cloud environments. SCATTERED SPIDER leverages leaked cloud authentication tokens [3], from publicly exposed code repositories like GitHub due to hardcoded credentials in application code. This allows attackers to use automated tools to scan and gain unauthorised access to cloud systems.
Figure 2 – Example of AWS token leak in GitHub
Phishing and Smishing Campaigns Target Cloud Services and High-Privileged Accounts
EclecticIQ analysts assess with high confidence that SCATTERED SPIDER is utilising phishing campaigns to compromise high-privileged user accounts, such as those of IT service desk administrators and cybersecurity teams. [4] These attacks focus on cloud-based services like Microsoft Entra ID and AWS EC2. Additionally, the group targets Software as a Service (SaaS) platforms such as Okta, ServiceNow, Zendesk, and VMware Workspace ONE by deploying phishing pages that closely mimic single sign-on (SSO) portals.
SCATTERED SPIDER has been using SMS phishing (smishing) techniques through text messages. Smishing, a form of phishing that uses SMS to deliver malicious links, has become a favoured tactic for cybercriminal group due to its ability to bypass traditional email filters and directly target users on their mobile devices. These campaigns have primarily targeted sectors, including financial services and insurance companies.

Figure 3 – Typosquatted domain and Phishing against
US-based financial services.
Smishing attacks target identity administrators in cloud infrastructures by prompting them to enter credentials for VMware Workspace ONE, a platform critical for application management and identity access policies. Smishing campaigns typically target victims through SMS messages, tricking them into clicking links that lead to phishing websites aimed at stealing login credentials and intercepting one-time passwords (OTPs). This allows attackers to gain unauthorised access even to accounts protected by multi-factor authentication (MFA).
EclecticIQ analysts observed that phishing pages used prompts, such as requesting employee ID and manager name to support social-engineering activities, particularly when impersonating employees during voice phishing calls.

Figure 4 – The EclecticIQ threat intelligence platform graph shows the
infrastructure pivoting from the HTML phishing template.
EclecticIQ analysts observed that SCATTERED SPIDER’s phishing domains predominantly use the .com and .net top-level domains (TLDs), often typosquatting legitimate organisations’ domain names. These domains typically include strings such as “ServiceNow”, “hr”, “corp”, “dev”, “okta”, “sso” and “workspace”.
EclecticIQ analysts assess with medium confidence that SCATTERED SPIDER has recently updated its tactics to avoid detection by shifting from using Autonomous System Numbers (ASN) like Porkbun and NAMECHEAP to the registrar registrar[.]eu.
Credential Stealers and Initial Access Brokers
EclecticIQ analysts observed the sale of authentication tokens and user credentials for cloud platforms like AWS, Azure, and GCP on Russian and English-speaking underground forums.
Figure 5 – AWS Tokens being sold on underground forms.
Credential stealers like Stealc, Raccoon Stealer, Vidar Stealer, and RedLine Stealer are used by SCATTERED SPIDER’s operations. These malware variants harvest cloud service authentication tokens, which are then sold on underground forums, including, but not limited to, RussianMarket and XSS. The acquired tokens provide attackers seamless access to cloud resources, bypassing traditional authentication.

Figure 6 – The initial access broker on the underground forum
is sharing a screenshot from the victim’s Entra ID.
Stealc infostealer searches explicitly data from the. aws and .azure directories in Windows endpoints, which typically contain configuration files and credentials for accessing these cloud services. Additionally, Stealc scans for the %LOCALAPPDATA%\.IdentityService\msal.cache file, where Azure Active Directory tokens are cached. Attackers can use these tokens to access cloud resources without going through the usual authentication processes.
SIM Swapping Techniques Used to Bypass MFA and Access SaaS Applications
The attackers use SIM swapping as a method to circumvent MFA, allowing them unauthorized access to critical SaaS platforms. In SIM swapping attacks, cybercriminal group deceive mobile carriers to transfer the victim’s phone number to their controlled SIM card. This allows them to collect MFA codes sent via SMS, effectively bypassing two-factor authentication. This method has been used to target user accounts on platforms like Okta, ServiceNow, and helpdesk systems.
Once inside a compromised user account, SCATTERED SPIDER targets cloud infrastructures like Microsoft Azure or AWS instances. In some cases, threat actors create unauthorised virtual machines (VMs) that bypass the victim’s security systems, as these newly created VMs often lack essential security or monitoring tools, such as endpoint detection and response (EDR). This allows the attackers to evade detection, steal data, and move laterally across the business network undetected.
The cybercriminal group abuses legitimate cloud tools such as Azure’s Special Administration Console and Data Factory to remotely execute commands, transfer data, and maintain persistence while avoiding detection.
EclecticIQ analysts have identified malicious SIM-swapping service providers operating on an underground marketplace hosted via a Telegram channel called the HSBC Network. These sellers, primarily teenagers based in the United Kingdom, actively offer malicious services targeting victims.

Figure 7 – Advertisement of a SIM swapping
service on the Telegram channel.

Figure 8 – SIM Swapping community on Telegram channel
called HSBC Network.
EclecticIQ analysts assess with high confidence that certain members and service sellers within the HSBC network are linked to the SCATTERED SPIDER group. This assessment is based on the observation of personas previously associated with SCATTERED SPIDER activity, which have been identified within the HSBC network and other well-known SIM-swapping communities on Telegram channels. Analysts noted that threat actors frequently use Telegram and Discord chat rooms to share tools and techniques, thereby enhancing their collective knowledge and capabilities.
Telecom Enemies: A Developer-as-a-Service Threat Group Empowering Phishing and Cyber Attacks
EclecticIQ analysts have identified a Developer-as-a-Service (DaaS) group called Telecom Enemies (also called Carrier or Telecom Clowns). Members of the SCATTERED SPIDER group have likely utilized this group to develop tools for malicious activities, such as Gorilla Call Bot, which is used for voice phishing campaigns by abusing Google Voice services.

Figure 9 – Advertised Gorilla callbot service on the Telegram
channel of the Telecom Enemies.
Figure 10 – Gorilla callbot controlled over Telegram bot.
EclecticIQ analysts observed that Telecom Enemies are selling Phishing kit services called Suite’s (All in one) AIO. Analysts identified the admin panel URL of the tool forward-icloud[.]com/admin/dashboard/login that is used as a shared platform between threat actors who bought their services. It is designed to deliver phishing templates for various services such as Coinbase, Gemini, Kraken, Binance, Robinhood, OKX, Trezor, Ledger, Exodus, MetaMask, Trust Wallet, Bitwarden, LastPass, Yahoo!, AOL, Microsoft/MSN, Gmail, and iCloud. Threat actors use Suite’s AIO dashboard to manage these phishing campaigns and collect 2FA tokens.

Figure 11 – Admin panel of the All-in-One Phishing Kit.
The tools and services offered by Telecom Enemies have been widely promoted on Telegram channels, including HSBC Network and Star Chat. These channels are actively used by SCATTERED SPIDER members, further amplifying the reach and accessibility of Telecom Enemies’ offerings within the underground community.
The group is well-integrated within underground forums, offering collaboration and development-for-hire services. Escrow and middleman services are accepted to facilitate secure transactions for threat actors.
Members of Telecom Enemies (@carrier / @TelecomEnemies #TE):
- @tempt
Aliases: “tempt,” “t0,” “bAS1C”
Specialties: Web app and API exploitation, reverse engineering, and network infiltration. AT&T, T-Mobile, and Verizon are particularly active in targeting carriers and mobile applications. - @swordartonline
Alias: “Lore”
Specialities: Web app and API exploitation, web crawling, and IoT penetration testing. - @someonesomewheresomething
Aliases: “PIN,” “u0”
Specialities: UEFI/firmware programming, Linux/NT driver development, and malware development. - @byte_array
Alias: “sp0m”
Specialties: Penetration testing, web app, and API exploitation.
Leveraging Open-Source Tools for Cloud Reconnaissance
Analysts observed that, after SCATTERED SPIDER gains access to a victim’s cloud infrastructure via SSO-enabled dashboards or Microsoft 365 (M365), they conduct reconnaissance to identify valuable data and resources.
SCATTERED SPIDER searches through integrated applications within the cloud environment, focusing on various applications, including Customer Relationship Management (CRM) systems, document management platforms, password storage solutions, project management tools, and code repositories. The goal is to identify information that can help them compromise additional accounts, escalate privileges, or move laterally across the network, thereby increasing their control over the victim’s systems.

Figure 12 – Example of the Cloud reconnaissance to
identify Global Admins.
Open-source tools such as AzureAD [5], ADExplorer [6], ADRecon [7], and PingCastle[8] are frequently used by SCATTERED SPIDER to gather information from corporate Active Directory (AD) [9]. These tools allow the adversary to create snapshots of AD databases, which can then be exfiltrated for further analysis. Figure 12 shows examples of reconnaissance behaviours on a real network.

Figure 13 – Example detections of
reconnaissance tools and scripts.
In their reconnaissance within M365, SCATTERED SPIDER is particularly interested in identifying:
- Password Management Tools: These tools can provide access to stored credentials, enabling further compromise of systems and accounts.
- Network Architecture Information: Understanding the network layout and virtual infrastructure helps the attackers target critical systems and potentially evade detection.
- Virtual Desktop Infrastructure (VDI) and VPN Configurations: Gaining access to these configurations allows the attackers to establish remote access and maintain persistence within the network.
- Privileged Access Management (PAM) Solutions: Access to these tools is critical for attackers to escalate their privileges within the organisation, allowing them to gain higher-level access to sensitive systems.
- Personnel Information: Identifying key internal contacts can be useful for social engineering attacks or for gathering additional information that supports further compromise.
Additionally, SCATTERED SPIDER seeks out information that can be leveraged for extortion or to target third-party entities associated with the victim. This includes:
- Third-Party Data: Accessing data related to customers or third-party services allows attackers to extend their impact beyond the initial victim, potentially compromising additional organisations.
- Data Supporting Extortion: Information such as cybersecurity insurance policies, personally identifiable information (PII), and financial records is valuable for determining ransom demands or conducting financially motivated attacks.
Through this comprehensive reconnaissance process, SCATTERED SPIDER positions itself to maximise the impact of their attacks, both within the victim organisation and across any connected third-party entities.
Persistence Access in Cloud Infrastructures
Abuse of Cross-Tenant Synchronization in Microsoft Entra ID
Since early 2024, EclecticIQ analysts have observed SCATTERED SPIDER abusing Cross-Tenant Synchronization (CTS) within Microsoft Entra ID (formerly Azure AD). [10] CTS is designed to facilitate seamless collaboration across different tenants by synchronising users and groups, helping organisations manage multiple tenants. Threat actors have leveraged this feature to establish persistence and maintain undetected access within compromised cloud environments.
Figure 14 – Cross-Tenant Synchronization attack in Azure.
Attack Methodology:
The abuse of CTS typically follows a systematic approach, enabling attackers to remain persistence access in a victim’s environment. The process generally involves:
- Compromising a Privileged Account: Attackers first gain access to an account within the victim tenant with sufficient privileges to alter cross-tenant settings. This is often a Global Administrator or Security Administrator role.
- Establishing Inbound Synchronization: The compromised account configures the victim tenant, allowing inbound synchronization from an attacker-controlled tenant. This effectively opens a pathway for user accounts from the attacker’s tenant to be provisioned into the victim tenant.
- Provisioning Malicious Accounts: With synchronization in place, the attacker can provision new malicious accounts within the victim tenant as needed. This allows for persistent access, even if initial accounts are detected and disabled.
- Lateral Movement Across Tenants: If the victim tenant has established CTS with other tenants, the attacker can leverage this setup to move laterally, potentially compromising additional environments.
The abuse of CTS enables attackers to blend malicious activities with legitimate operations, reducing the likelihood of detection. Synchronized accounts can be used to perform a range of malicious actions, including data exfiltration and privilege escalation. [11]
Leveraging Federated Identity Providers for Persistent Access
Federated identity providers in Microsoft Entra ID and Okta tenants allow organisations to delegate authentication to external identity providers (IdPs), simplifying system access management. However, SCATTERED SPIDER abuses this feature to maintain persistence and escalate privileges within compromised environments.
Attack Methodology:
The abuse of federated identity providers typically involves the following steps:
- Compromising a High-Privilege Account: Attackers gain access to an account with the authority to modify federated domain settings, such as a Global Administrator or Security Administrator.
- Creating a Malicious Federated Domain: The compromised account is used to either create a new federated domain or alter an existing one, configuring it to authenticate through a malicious IdP controlled by the attacker.
- Generating Forged Authentication Tokens: The attacker generates forged Security Assertion Markup Language (SAML) tokens, a tactic known as “Golden SAML,” allowing them to impersonate any user within the tenant, including those with multi-factor authentication (MFA).
- Maintaining Persistence: The attacker manages the federated domain settings to ensure continued access. Even if the initial compromised account is disabled, the federated domain serves as a backdoor, enabling re-entry.
- Facilitating Lateral Movement: By leveraging trust relationships and federation settings, attackers can move laterally across connected tenants, expanding their reach within the cloud infrastructure, accessing sensitive data, or further escalating privileges.
Remote Access and Control: Leveraging RMM and Protocol Tunnelling Tools
To maintain control over compromised environments, SCATTERED SPIDER employs a variety of Remote Desktop and Remote Monitoring and Management (RMM) tools, as well as protocol tunnelling and proxy tools. These enable them to interact with hosts across the victim’s network and obscure their activities.
- Remote Desktop and RMM Tools: SCATTERED SPIDER deploys a range of RMM tools, including AnyDesk, TeamViewer, RustDesk, and MeshCentral. These tools allow the adversary to establish remote connections to victim hosts, facilitating lateral movement and persistent control.
- Protocol Tunnelling and Proxy Tools: MobaXterm, Ngrok, and Proxifier are used by SCATTERED SPIDER to establish SSH connections and create reverse proxies. These tools enable the adversary to bypass network defences and maintain a presence within the victim’s environment, often using these tunnels to communicate with compromised systems securely.
Impairing Security Tools and Defence Evasion
SCATTERED SPIDER employs techniques to evade detection and disable security measures within targeted environments. These methods bypass enterprise security defences, enabling the adversary to maintain a foothold and execute malicious activities with minimal interference.
- Residential Proxies: SCATTERED SPIDER utilizes residential proxies such as NSOCKS and Faceless to hide their true IP address. This tactic makes it appear as though they are logging into victim accounts from the same geographical area as the legitimate account owner, helping them evade detection mechanisms like “impossible travel” alerts.
- Using Victim Security Tooling: By compromising accounts with SSO-enabled access to endpoint detection and response (EDR) tools, SCATTERED SPIDER gains the ability to disable detections on compromised hosts. The adversary also uses the remote shell functionality of these tools for network reconnaissance and the deployment of remote management tools.
- Disabling Security Tools: SCATTERED SPIDER often employs publicly available scripts, such as privacy-script.bat, to disable Microsoft Defender functionalities and modify Windows Firewall settings [12]. This typically occurs just before deploying ransomware to minimise the risk of detection.
- Creating Virtual Machines: To further evade detection and maintain persistence, SCATTERED SPIDER creates custom virtual machines (VMs) in cloud environments such as AWS, Azure, and VMware. These VMs are used as unmanaged hosts within the network, allowing the adversary to stage tools and access other network hosts remotely.
- Malicious Mail Transport Rules: SCATTERED SPIDER configures mail transport rules in victim Microsoft 365 (M365) tenants to redirect security-related emails to adversary-controlled addresses. This prevents the victim organisation from receiving suspicious activity alerts or security notifications.
- Rebooting in Safe Mode: The adversary reboots systems into Safe Mode using the bcdedit command to disable or uninstall protected services, including security products. This mode gives them greater flexibility to operate within the victim environment without interference.
Credential Access Tactics: Exploiting Active Directory and Cloud Identity Systems
SCATTERED SPIDER leverages various tools and techniques to gain unauthorised access to credentials within traditional Active Directory (AD) environments and cloud-based identity systems like Microsoft Entra ID (Azure AD). This access enables the adversary to escalate privileges and maintain persistence across the victim’s infrastructure.
- Cloud Identity Exploitation: SCATTERED SPIDER uses scripts to enumerate and remove Multi-Factor Authentication (MFA) methods from compromised accounts in Microsoft Entra ID. By resetting MFA, the adversary reduces the chances of blocking their activities by additional authentication measures.
- Credential Dumping: The adversary often uses tools like GoSecretsDump [13] to extract password hashes and Kerberos keys from domain controllers. This is typically done after creating snapshots of victim servers in Azure or VMware environments, which are then mounted to adversary-controlled machines.
- Cookie Access: To maintain access to cloud services, SCATTERED SPIDER utilises browser extensions like Cookie Quick Manager and EditThisCookie to steal session cookies, allowing them to authenticate to services like Microsoft 365 (M365) without needing to re-enter credentials.
Exfiltration Tactics: Leveraging Remote Storage and ETL Tools
SCATTERED SPIDER employs various data exfiltration techniques to collect sensitive information from victim environments such as AWS S3 bucket and M365 SharePoint data. Threat actors often utilise remote storage services and Extract Transform Load (ETL) tools to facilitate this process.
- Remote Storage Services: SCATTERED SPIDER frequently downloads and uploads data to remote storage services such as S3 buckets, BackBlaze, and other cloud storage solutions. The adversary uses tools like S3 Browser to manage these operations, ensuring that large volumes of data can be exfiltrated with minimal detection.

Figure 15 – Linux version of the BlackCat Ransomware
downloading itself from BlackBaze.
- ETL Tools: SCATTERED SPIDER uses ETL tools like AirByte, S3 Browser, and Stitch to synchronise and exfiltrate data from victim environments. These tools are often configured using compromised email addresses to create accounts that facilitate data transfer from internal systems like ZenDesk Support and Salesforce to attacker-controlled servers.
- Additional Techniques: SCATTERED SPIDER has also been observed using compromised email addresses to send data directly to attacker-controlled accounts, uploading victim data to GitHub repositories, and utilising file-sharing services such as filedropper[.]com and file[.]io to exfiltrate sensitive information.
SCATTERED SPIDER Shifts Focus to Cloud IaaS, Targeting VMware ESXi and Azure for Ransomware Deployments
SCATTERED SPIDER has focused on deploying ransomware in cloud environments, mainly targeting VMware vSphere ESXi infrastructure as a service (IaaS). Their deployment tactics are often automated, leveraging customised scripts to execute the ransomware payloads efficiently.
- Targeting VMware ESXi: SCATTERED SPIDER deploys AlphV ransomware binaries on ESXi hosts. The execution of ransomware is automated by passing specific arguments and targeting IP addresses defined in the ransomware configuration.
- Automated Deployment via Azure: In late 2023, SCATTERED SPIDER was observed using Azure’s Run Command to execute shell scripts that deployed ransomware within an Azure tenant. These scripts were designed to stop security services, download the ransomware executable from cloud storage, and execute it, effectively encrypting the victim’s data with minimal intervention.
- Persistence and Control: To maintain control and ensure the ransomware deployment is successful, SCATTERED SPIDER often alters the root passwords on VMware ESXi hypervisors and may disable security tools before executing the ransomware. This makes recovery efforts more challenging for the victim.
Prevention Opportunities
Authentication and Account Security
- Secure Authentication:
- Implement SIM Swapping Proof MFA: Enforce using Microsoft Authenticator with number matching, removing SMS as an MFA verification option to prevent SIM swapping attacks and enhance security against common TTPs used by threat actors.
- Enforce Conditional Access Policies: Enforce Conditional Access Policies to restrict access to critical systems. For instance, it requires MFA for all users and especially for administrators, ensuring phishing-resistant MFA types such as Windows Hello for Business.
- Multi-Factor for Sensitive Actions: Mandate two authentication methods for sensitive operations, like password resets or MFA changes, and require video verification for user identity confirmation during such processes.
- Limit Account Permissions: Ensure low-privileged user accounts are restricted from modifying account or security policies and utilize segregated admin accounts to prevent privilege escalation.
- Monitoring and Alerts:
- Detect Suspicious Behaviour: Monitor for unusual patterns, such as high-risk sign-ins or changes in password reset requests, especially outside business hours. Implement alerts for key activities, including Windows logon password changes or unauthorised MFA device registrations.
- Cloud Activity Monitoring: Track and analyse cloud environment changes, such as firewall modifications, high egress traffic, or an unusual number of API calls, which could indicate adversarial movements or service enumeration.
- Out-of-Band Communication:
- Secure Communication Channels: In suspected compromise scenarios, use out-of-band communication channels for critical exchanges. Implement video calls with identity verification as a standard for helpdesk operations, particularly for password or MFA reset requests.
Cloud Environment Security
- Hypervisor and Cloud Resource Security:
- Restrict Access: Disable SSH access to VMware ESXi hosts, enable Lockdown mode, and segment ESXi management interfaces to minimize unauthorized access risks. Limit cloud administrative roles through Conditional Access policies that enforce secure login methods and device compliance.
- Audit and Control: Regularly audit domain and local accounts, focusing on identifying and limiting privileged account credentials that could be exploited by adversaries.
- Monitoring Cloud Activities:
- Track Cloud Changes: Continuously monitor for the creation of new virtual machines, modifications in firewall rules, and high volumes of egress traffic. Establish alerts for anomalies that could signal a breach or an attack in progress, such as the enumeration of administrative accounts.
- Backup and Snapshot Management:
- Protect Backups: Monitor for any snapshot deletions and configure alerts to identify and respond to potential ransomware activities aimed at eliminating backups to maximize damage.
Data Security and Incident Response
- Firewall and Network Security:
- Restrict Network Access: Limit broad inbound/outbound internet access to hypervisors, domain controllers, and other critical systems. Employ Conditional Access Policies to restrict administrative access based on trusted network locations and device compliance.
- Secure Remote Services: Disable unnecessary remote services and enforce centralized access through secure proxies, gateways, or managed remote access systems like VPNs.
- Data Integrity:
- Enable and Monitor Logging: Ensure logging is enabled for critical data warehousing solutions and monitor for high egress traffic that could indicate data exfiltration attempts by adversaries.
- Response to On-Premises Threats:
- Implement On-Premises Eviction: In cases of suspected compromise, follow a structured recovery process, including Active Directory Forest Recovery, mass password resets, and thorough reviews of Access Control Lists (ACLs) to eliminate adversary footholds.
Phishing and Social Engineering
- Phishing Domains:
- Regularly monitor for typosquatting domains like your organization’s legitimate domains, especially those targeting your cloud environments. Proactively secure these domains to prevent phishing attacks and social engineering tactics.
Privileged Access Management:
- Enforce Approval Processes: Require multi-user approvals for sensitive roles such as Global Administrator. Continuously monitor for the creation of new privileged users or changes in authentication factors to prevent unauthorised privilege escalation.
KQL Queries for Detection
Cross-Tenant Access Partner Addition Audit: Monitoring for unauthorized or suspicious changes to tenant access settings in Azure AD by tracking the operation, initiating user, and involved tenants.
AuditLogs | where OperationName == “Add a partner to cross-tenant access setting” | extend modifiedProperties = parse_json(tostring(TargetResources[0].modifiedProperties)) | where modifiedProperties[0].displayName == “tenantId” | extend initiating_user = tostring(parse_json(tostring(InitiatedBy.user)).userPrincipalName), source_ip = tostring(parse_json(tostring(InitiatedBy.user)).ipAddress), target_tenant = tostring(modifiedProperties[0].newValue) | project TimeGenerated, OperationName, initiating_user, source_ip, source_tenant = AADTenantId, target_tenant |
Managed Identity Federated Credentials Abuse Detection: Use the AzureActivity or similar logs to detect when a federated credential is added to a Managed Identity. Look for operations indicating the creation of these credentials and potentially correlate these events with known trusted sources or entities.
| // Detecting Suspicious Federated Domain Changes and Token Issuance let suspiciousDomains = materialize( AuditLogs | where ActivityDisplayName == “Set domain authentication” | where TargetResources[0].ModifiedProperties has_any (“Federation settings”, “Federated domain”) | project TimeGenerated, InitiatedBy, TargetResources );let highPrivilegeAccounts = materialize( SigninLogs | where ConditionalAccessPolicies has_any (“Global Administrator”, “Security Administrator”) | project UserPrincipalName, AppDisplayName, IPAddress, TimeGenerated );let suspiciousTokenIssuance = materialize( SigninLogs | where AuthenticationDetails has “Security Assertion Markup Language (SAML)” | extend isMFA = iff(AuthenticationDetails has “Multi-Factor Authentication”, “True”, “False”) | where isMFA == “False” | project TimeGenerated, UserPrincipalName, AppDisplayName, IPAddress, AuthenticationDetails );// Join the suspicious domain modifications with high privilege account sign-ins suspiciousDomains | join kind=inner (highPrivilegeAccounts) on $left.InitiatedBy == $right.UserPrincipalName | extend suspiciousActivity = “Federated domain modified by high-privilege account” | union ( // Join suspicious SAML token issuance with high privilege account sign-ins suspiciousTokenIssuance | join kind=inner (highPrivilegeAccounts) on $left.UserPrincipalName == $right.UserPrincipalName | extend suspiciousActivity = “Suspicious SAML token issued by high-privilege account” )| project TimeGenerated, InitiatedBy, TargetResources, suspiciousActivity, IPAddress | order by TimeGenerated desc |
RMM Software Detection Query: Use the DeviceProcessEvents logs to detect processes associated with Remote Monitoring and Management (RMM) software. This query filters for events within a specified timeframe, focusing on processes from known RMM software vendors. It excludes activities from devices on a predefined exclusion list and then sorts the results by timestamp, enabling you to quickly identify and investigate potentially unauthorized RMM software usage.
| let RMMSoftware = externaldata(RMMSoftware: string) [@”https://raw.githubusercontent.com/cyb3rmik3/Hunting-Lists/main/rmm-software.csv” with (format=”csv”, ignoreFirstRecord=True); let ExcludedDevices = datatable(DeviceName: string) // Add as many devices as you want to exclude [ “DeviceName1”, “DeviceName2”, “DeviceName3” ];let Timeframe = 7d; // Adjust the timeframe to suit your investigation needsDeviceProcessEvents | where Timestamp > ago(Timeframe) | where ProcessVersionInfoCompanyName has_any (RMMSoftware) | where not(DeviceName in (ExcludedDevices)) | project Timestamp, DeviceName, ActionType, FileName, FolderPath, ProcessVersionInfoCompanyName, ProcessVersionInfoProductName, ProcessCommandLine, AccountName, InitiatingProcessAccountName, InitiatingProcessFileName, InitiatingProcessCommandLine | sort by Timestamp desc; |
Indicator of Compromises (IOCs)
| Indicator | Type | Malware Families |
| c7497366fd0d8c9d72f96e7190632a51 | MD5 | Gosecretsdump |
| b233ff9dcf5520d69f9b75e1424f3271 | Sliver | |
| cc230dcea35be180e3487b53e4b2cfba | BlackCat Ransomware | |
| 8445274c237eb83d56070e499f43641f | Phishing HTML Template | |
| 1d05a83a639031913574c0bbb06026a4 | Phishing HTML Template | |
| 586bd54b564926682b75330b190cbace | Phishing HTML Template |
Phishing Domains:
| Indicator | Registrar Name |
| revolut-ticket[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| servicenow-help[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| ibexglobai[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| authenticate-bt[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| securian-hr[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| creditkarma-help[.]com | Hosting Concepts B.V. d/b/a Registrar.eu |
| login[.]uscc-hr[.]com | AS-CHOOPA |
| taskus[-]sso[.]com | AS-CHOOPA |
| login[.]five9-hr[.]com | DIGITALOCEAN-ASN |
Structured Data
Find this and other research in our public TAXII collection for easy use in your security stack: https://cti.eclecticiq.com/taxii/discovery.
Please refer to our support page for guidance on how to access the feeds.
About EclecticIQ Intelligence & Research Team
EclecticIQ is a global provider of threat intelligence, hunting, and response technology and services. Headquartered in Amsterdam, the EclecticIQ Intelligence & Research Team is made up of experts from Europe and the U.S. with decades of experience in cyber security and intelligence in industry and government.
We would love to hear from you. Please send us your feedback by emailing us at research@eclecticiq.com.
You might also be interested in
EclecticIQ Intelligence Center 3.4 is here
ONNX Store: Phishing-as-a-Service Platform Targeting Financial Institution
References
[1] “Scattered Spider | CISA.” Accessed: Sep. 03, 2024. [Online]. Available: https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320a
[2] “#StopRansomware: ALPHV Blackcat | CISA.” Accessed: Sep. 03, 2024. [Online]. Available: https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-353a
[3] “Scattered Spider: The Modus Operandi.” Accessed: Sep. 04, 2024. [Online]. Available: https://www.trellix.com/blogs/research/scattered-spider-the-modus-operandi/
[4] Josue, “Eight-legged Phreaks: Silent Push DNS and content scans discover new Scattered Spider phishing infrastructure. – Silent Push.” Accessed: Aug. 26, 2024. [Online]. Available: https://www.silentpush.com/blog/scattered-spider/, https://www.silentpush.com/blog/scattered-spider/
[5] “AzureAD 2.0.2.182.” Accessed: Aug. 27, 2024. [Online]. Available: https://powershellgallery.com/packages/AzureAD/
[6] markruss, “AD Explorer – Sysinternals.” Accessed: Aug. 27, 2024. [Online]. Available: https://learn.microsoft.com/en-us/sysinternals/downloads/adexplorer
[7] sense-of-security/ADRecon. (Aug. 26, 2024). HTML. Sense of Security. Accessed: Aug. 27, 2024. [Online]. Available: https://github.com/sense-of-security/ADRecon
[8] netwrix/pingcastle. (Aug. 25, 2024). C#. Netwrix Corporation. Accessed: Aug. 27, 2024. [Online]. Available: https://github.com/netwrix/pingcastle
[9] “Why Are You Texting Me? UNC3944 Leverages SMS Phishing Campaigns for SIM Swapping, Ransomware, Extortion, and Notoriety,” Google Cloud Blog. Accessed: Aug. 26, 2024. [Online]. Available: https://cloud.google.com/blog/topics/threat-intelligence/unc3944-sms-phishing-sim-swapping-ransomware
[10] “Octo Tempest: Hybrid identity compromise recovery,” TECHCOMMUNITY.MICROSOFT.COM. Accessed: Aug. 26, 2024. [Online]. Available: https://techcommunity.microsoft.com/t5/microsoft-security-experts-blog/octo-tempest-hybrid-identity-compromise-recovery/ba-p/4166783
[11] “Cross-Tenant Impersonation: Prevention and Detection,” Okta Security. Accessed: Aug. 27, 2024. [Online]. Available: https://dev-oktaweb-jsonapi.pantheonsite.io/articles/2023/08/cross-tenant-impersonation-prevention-and-detection
[12] “Scattered Spider Targets SaaS Platforms For Data Exfiltration,” Decipher. Accessed: Sep. 04, 2024. [Online]. Available: https://duo.com/decipher/scattered-spider-group-eyes-saas-platforms-for-data-exfiltration
[13] C_Sto, C-Sto/gosecretsdump. (Aug. 15, 2024). Go. Accessed: Aug. 28, 2024. [Online]. Available: https://github.com/C-Sto/gosecretsdump