
Infostealers Webinar – Hudson Rock
Learn about Infostealers with actual real life breaches caused by Infostealer infections with Leonid Rozenberg, Hudson Rock’s Head of Partnerships & Integrations. To discover how
Home » You searched for hudson rock

Learn about Infostealers with actual real life breaches caused by Infostealer infections with Leonid Rozenberg, Hudson Rock’s Head of Partnerships & Integrations. To discover how

Hudson Rock’s data exploration capabilities allow for seamless analysis of massive amounts of assets associated with Infostealer infections. In this example, we analyze all domains
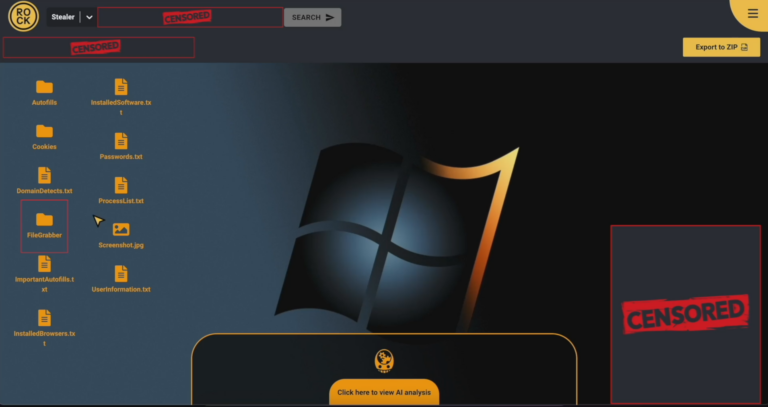
Hudson Rock’s Infostealer Investigation Module provides cybersecurity professionals the ability to investigate all the data captured from an Infostealer infection of employees and customers at

Hudson Rock’s database, with tens of millions of computers infected worldwide, enables cybersecurity and law enforcement customers to investigate suspicious infected computers that are using

In this Help Net Security interview, Alon Gal, CTO at Hudson Rock, discusses integrating cybercrime intelligence into existing security infrastructures. Our discussion will cover a range
Introduction Hudson Rock recently shed light on how a compromised Citrix account without MFA was potentially used to deploy a devastating ransomware attack on Change Healthcare. This
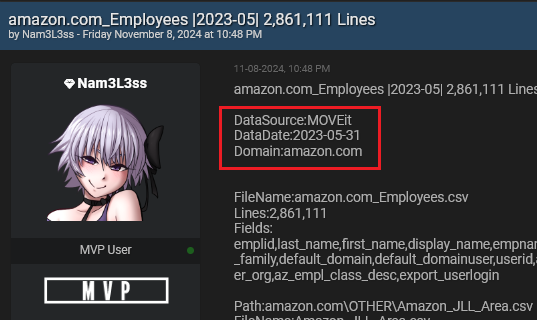
Written by Alon Gal A person operating under the username Nam3L3ss has exploited a critical vulnerability in MOVEit, a file transfer software, exposing extensive employee
In this new episode of the mnemonic security podcast, Robby Peralta is joined by Leonid Rozenberg, a cybersecurity expert and dark web researcher at Hudson

Free Infostealer Intelligence Tools by Hudson Rock – www.hudsonrock.com/free-tools On November 4th, Schneider Electric acknowledged a data breach in which hackers stole 40GB of data
Disclaimer: Hudson Rock does not insinuate or imply responsibility or liability on behalf of any parties mentioned herein. The content is intended solely for informational
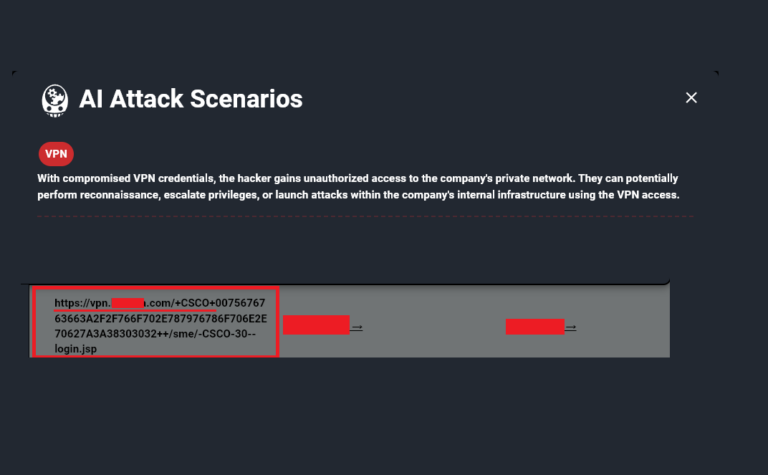
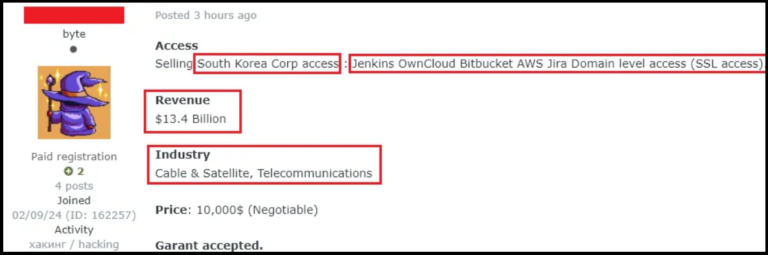
We are now at a point where numerous cyberattacks have been carried out using compromised Infostealer data. Major companies such as AT&T, Ticketmaster, Orange, Airbus,
Interview with Malware Protection expert Leonid Rozenberg with Hudson Rock (www.hudsonrock.com) on exposing information stealers, protecting identities online, hackers who sell vulnerabilities, and how to

Phishing email campaign targets Taiwan Talos observed an unknown threat actor conducting a malicious phishing campaign targeting victims in Taiwan since at least July 2024.
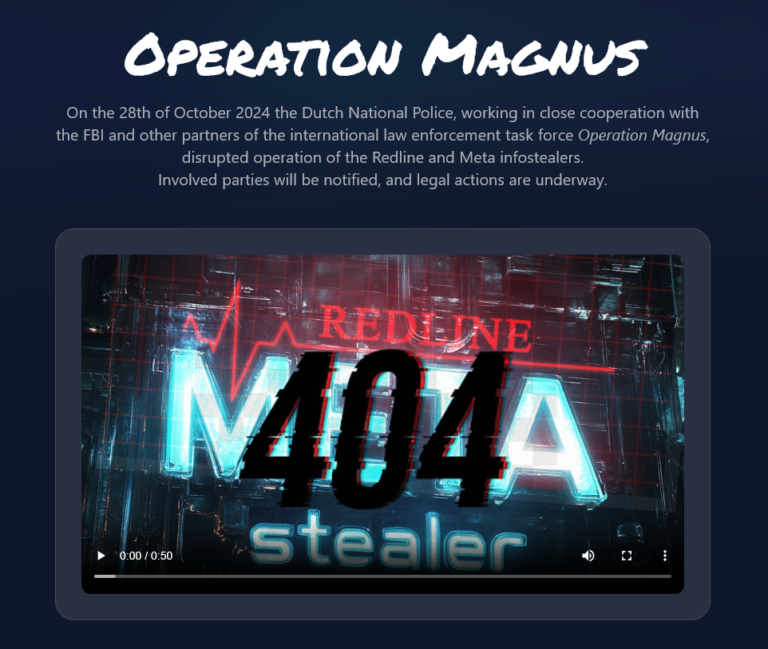
*Not fully confirmed yet According to the website which was discovered through Redline related Telegram channels, law enforcement was able to hack the infrastructure of
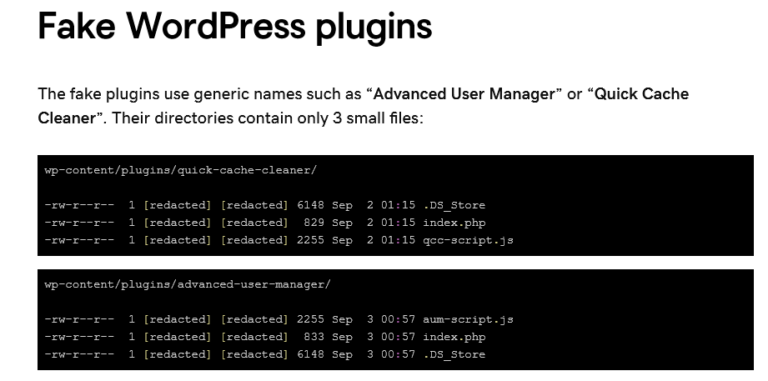
Key findings Overview The GoDaddy Security team is tracking a new variant of ClickFix (also known as ClearFake) fake browser update malware that is distributed via bogus WordPress
Stay informed with the latest insights in our Infostealers weekly report. Explore key findings, trends and data on info-stealing activities.
