Identity Behind Massive Discord Spying Tool Revealed due to Infostealer Infection
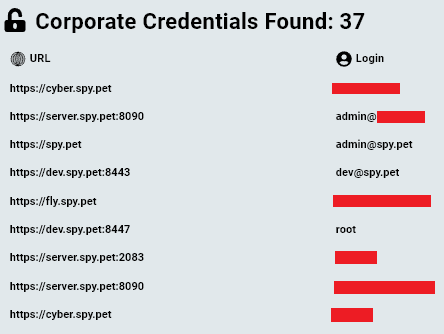
This article aims to shed light on the identity behind a massive Discord spying tool and raise concerns about the possibility of private Discord data being accessed by hackers. Intro A controversy surrounding the anonymously-run website spy.pet has recently made headlines, raising serious privacy concerns. The website is designed to enable anyone to access messages […]
Single Citrix Compromised Credential Results in $22,000,000 Ransom to Change Healthcare
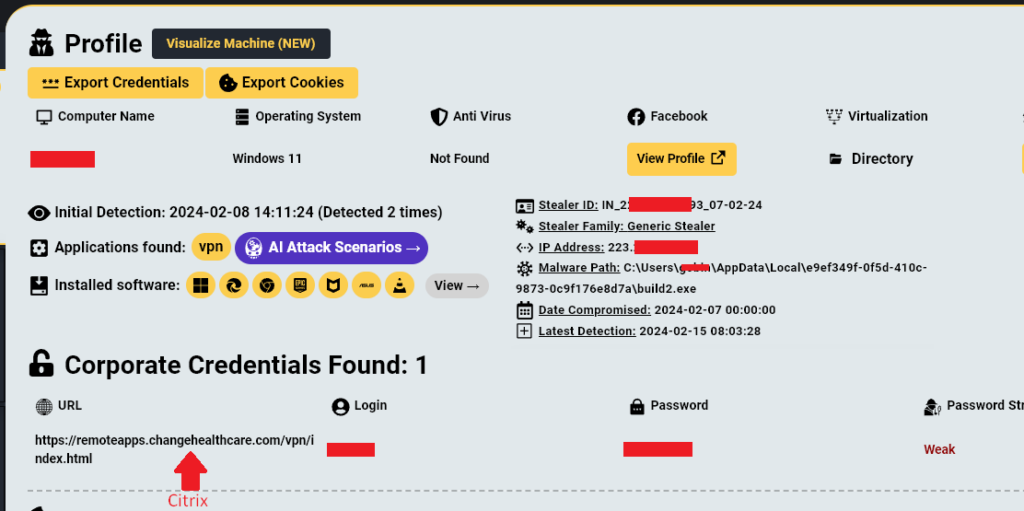
In late February 2024 Change Healthcare suffered a devastating ransomware attack which led to major disruptions to the company’s platform, estimated at a staggering $872,000,000 The attack which was carried out by BlackCat ransomware group also resulted in a $22,000,000 ransom payment. But how did this happen? In a testimony by Andrew Witty, Change Healthcare’s […]
Distribution of Infostealer Made With Electron
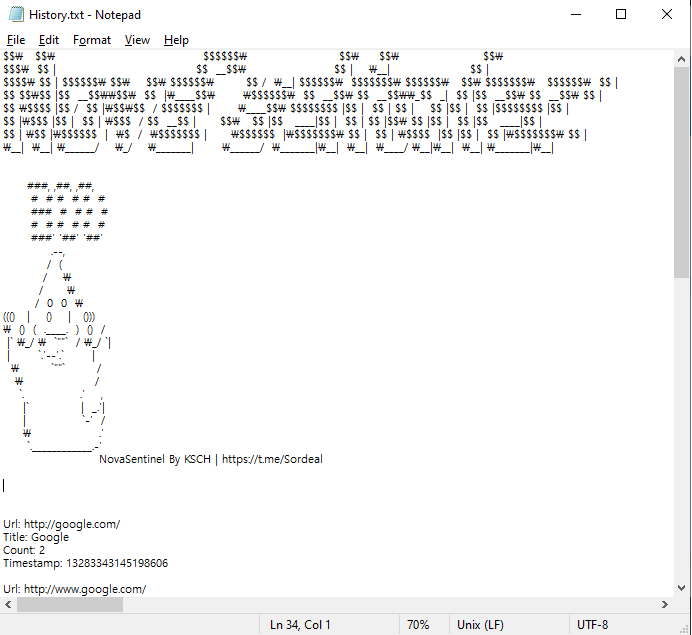
AhnLab SEcurity intelligence Center (ASEC) has discovered an Infostealer strain made with Electron. Electron is a framework that allows one to develop apps using JavaScript, HTML, and CSS. Discord and Microsoft VSCode are major examples of applications made with Electron. Apps made with Electron are packaged and usually distributed in Nullsoft Scriptable Install System (NSIS) […]
Redline Stealer: A Novel Approach
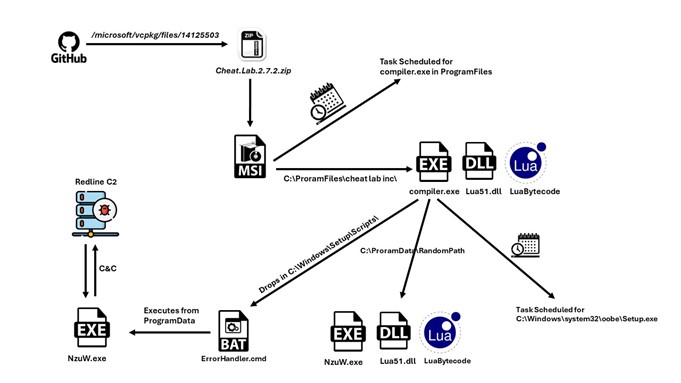
A new packed variant of the Redline Stealer trojan was observed in the wild, leveraging Lua bytecode to perform malicious behavior.McAfee telemetry data shows this malware strain is very prevalent, covering North America, South America, Europe, and Asia and reaching Australia. Infection Chain Source: Add a Custom Script to Windows Setup | Microsoft Learn We can […]
CoralRaider targets victims’ data and social media accounts

CoralRaider operators likely based in Vietnam Talos assesses with high confidence that the CoralRaider operators are based in Vietnam, based on the actor messages in their Telegram C2 bot channels and language preference in naming their bots, PDB strings, and other Vietnamese words hardcoded in their payload binaries. The actor’s IP address is located in […]
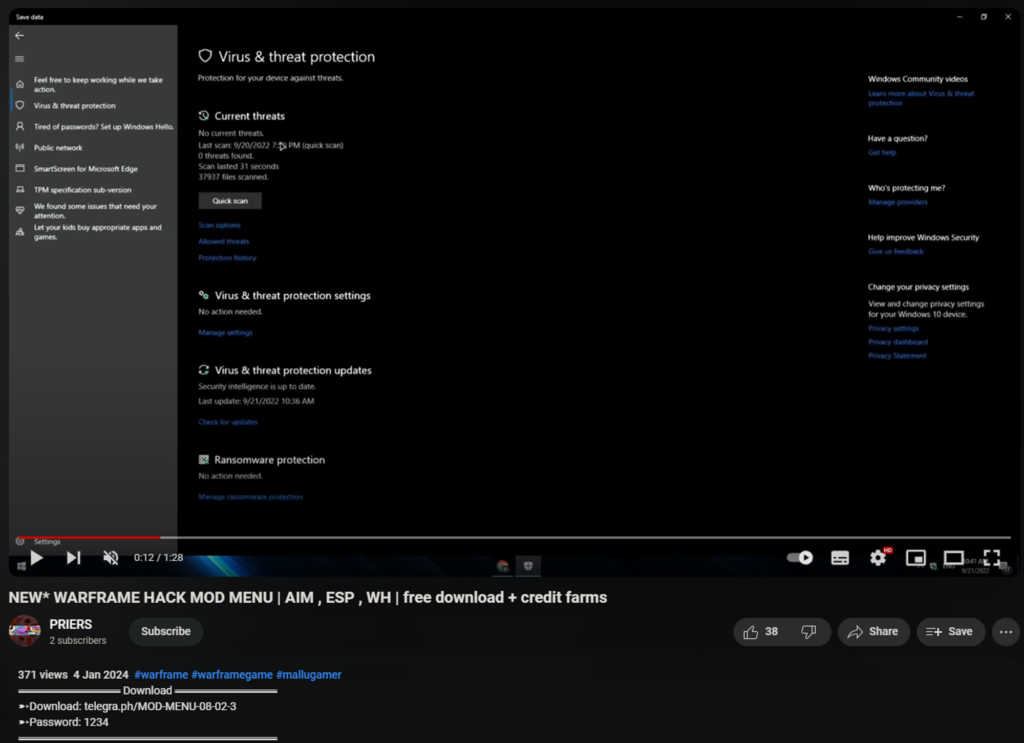
Activision: Enable 2FA to secure accounts recently stolen by malware

An infostealer malware campaign has collected millions of logins from users of various gaming websites, including players that use cheats, pay-to-cheat services. The details emerged after Zebleer, the developer of Phantom Overlay cheats for Call of Duty and Counter-Strike, apparently found an infostealer database. “The DB for the stealer represents gaming related accounts much more than […]
PyPI halts new projects, users for 10 hours due to infostealer influx

A few hours ago, The Python Package Index (PyPi) suspended new project creation and new user registration to mitigate an ongoing malware upload campaign. The research team of Checkmarx simultaneously investigated a campaign of multiple malicious packages appear to be related to the same threat actors. The threat actors target victims with Typosquatting attack technique […]
Extra credit: VietCredCare information stealer takes aim at Vietnamese businesses

Group-IB discovers new information stealer targeting Vietnam with rare functionality to filter out Facebook accounts with advertising credits…
The Darker Side of Stealer Malware: A Consumer Nightmare
Falling victim to an infostealer, such as Redline, is arguably one of the biggest threats to consumers—individual users who might seem less lucrative targets compared to businesses. Traditional malware often targets enterprises, banking on their urgency to maintain operations and their capacity to pay hefty ransoms. Consumers, on the other hand, might find it more […]
The Rise of Infostealer Data in Propaganda and Fraud

What do Andrew Tate, a Pro-Palestine hacking group, and AnyDesk all have in common? For a while now, Infostealer credentials data has been used as a means for disinformation, propaganda, or to facilitate fraud. Here are some recent examples Hudson Rock was able to discover: 1. Haghjoyan Hacking Group Cyberwar Disinformation. Their Claim: On october […]
Exploring the Latest Mispadu Stealer Variant

Executive Summary Unit 42 researchers recently discovered activity attributed to Mispadu Stealer, a stealthy infostealer first reported in 2019. We found this activity as part of the Unit 42 Managed Threat Hunting offering. We discovered this threat activity while hunting for the SmartScreen CVE-2023-36025 vulnerability. When we hunted for exploitation of the CVE-2023-36025 vulnerability in […]
PONY | FAREIT. Stealer, Loader, and Botnet.

_OVERVIEW Pony (also known as Fareit or Siplog) is a malware categorized as a loader and stealer, although it is also used as a botnet, being a tool that has been used for more than 10 years and is still in use. This infamous malware continues to receive updates and can be purchased, and has […]