By [Alon Gal] | April 2025
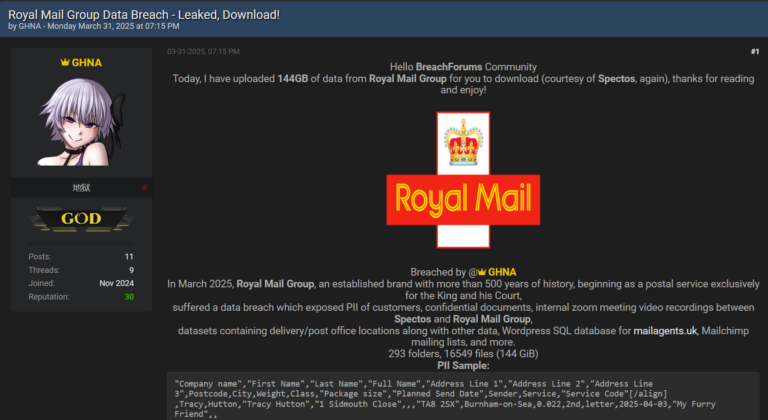
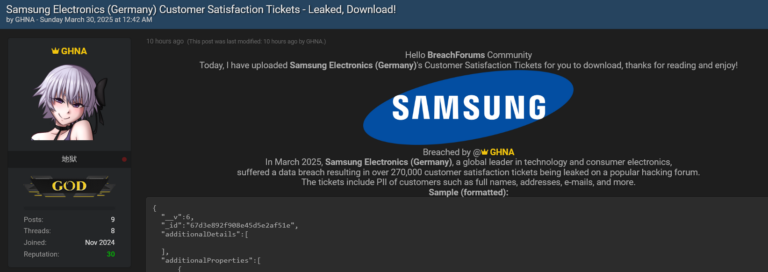
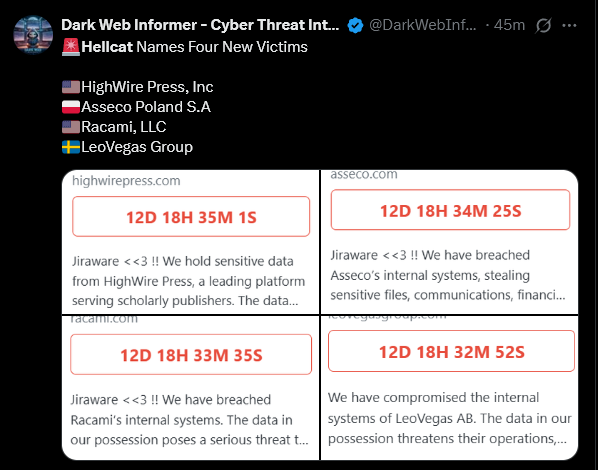
The HellCat ransomware group has once again demonstrated their relentless focus on exploiting Jira credentials stolen through infostealer malware, targeting four new organizations: HighWire Press, Asseco, Racami, and LeoVegas Group.
Hudson Rock has been tracking HellCat’s activities since their emergence. Research conducted by Hudson Rock confirms that all four breaches stem from compromised Jira credentials harvested by infostealers, a pattern observed in HellCat’s earlier attacks on Jaguar Land Rover, Telefonica, Schneider Electric, Orange, and others.
This article explores the details of these latest attacks, the role of infostealer malware, and actionable steps organizations can take to protect themselves.
HellCat’s Latest Victims: A Global Hacking Spree
On April 5, 2025, HellCat published their latest victims, showcasing their signature tactic of targeting Atlassian Jira instances with stolen credentials. The four organizations named in the post are:
- HighWire Press, Inc. (USA), a leading platform serving scholarly publishers.
- Asseco Poland S.A. (Poland), a major IT solutions provider in Europe.
- Racami, LLC (USA), a technology firm specializing in customer communications management.
- LeoVegas Group (Sweden), a prominent online gaming and betting company.
Each breach announcement included a countdown timer (e.g., “12D 18H 35M 1S” for HighWire Press) and a message from HellCat, signed with a trademark “Jiraware < < 3!!” tagline. The group claims to have stolen sensitive data, including internal files, communications, and financial records, and is threatening to leak or sell the information if their demands are not met.
This follows HellCat’s established playbook, which Hudson Rock researchers have documented extensively: gain access through compromised Jira credentials, exfiltrate data, and then extort the victim.
HellCat’s focus on Jira is not coincidental. As noted in Hudson Rock’s previous article on the Jaguar Land Rover breach (source), Atlassian Jira is a prime target for attackers due to its centrality in enterprise workflows and the wealth of sensitive data it houses. Once inside, threat actors like HellCat can move laterally, escalate privileges, and extract critical information with alarming ease.
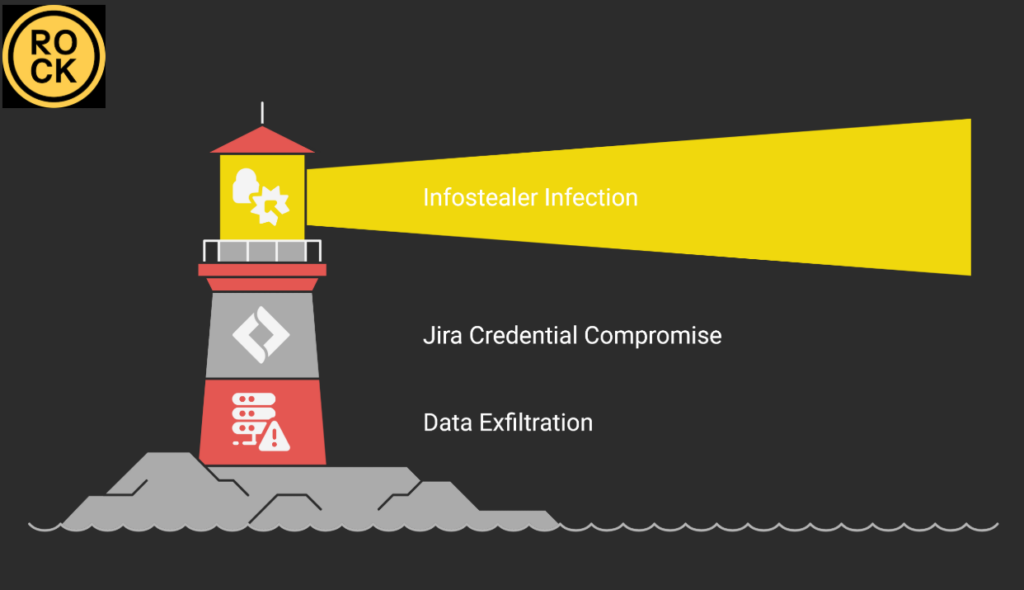
The Infostealer Connection: How HellCat Gains Access
HellCat’s attacks are a textbook example of how infostealer malware fuels ransomware operations. Infostealers are a type of malware designed to harvest credentials, authentication cookies, and other sensitive data from infected devices. These stolen credentials are then sold on the dark web or used directly by groups like HellCat to target high-value systems. In the case of Jira, compromised credentials often provide a direct gateway to an organization’s most sensitive data and systems.
Hudson Rock’s cybercrime intelligence database, built from analyzing over 30,000,000 systems infected with infostealers, has revealed that thousands of organizations have Jira-related credentials exposed through infostealer infections. HellCat has capitalized on this vulnerability, as confirmed by a recent report from BleepingComputer (source), which highlighted the group’s “worldwide Jira hacking spree” using stolen credentials.
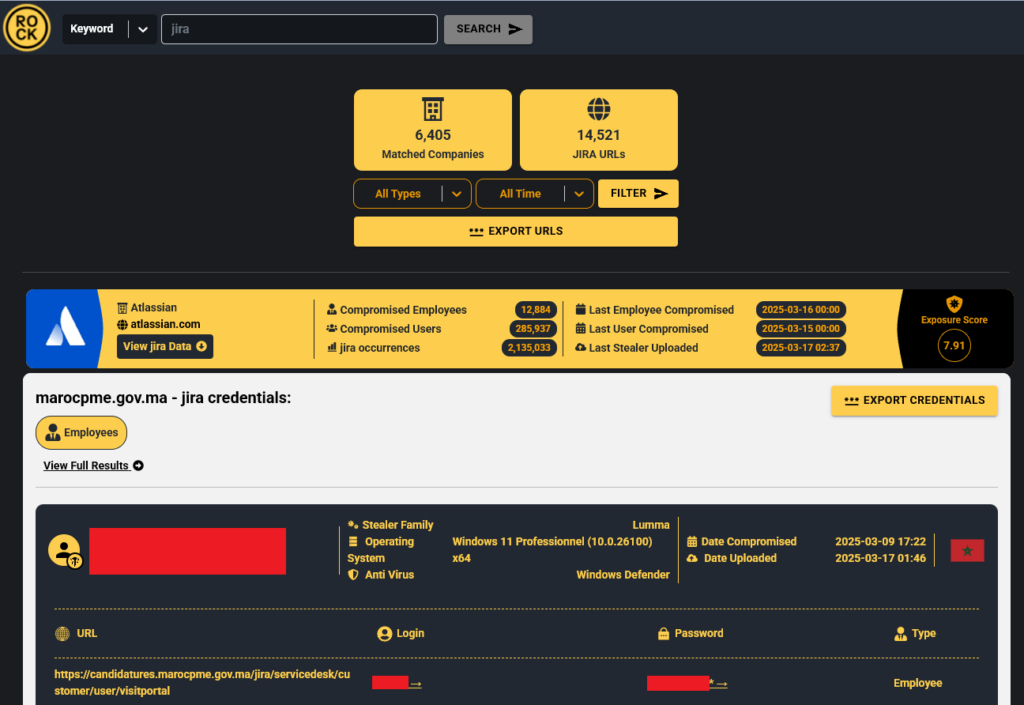
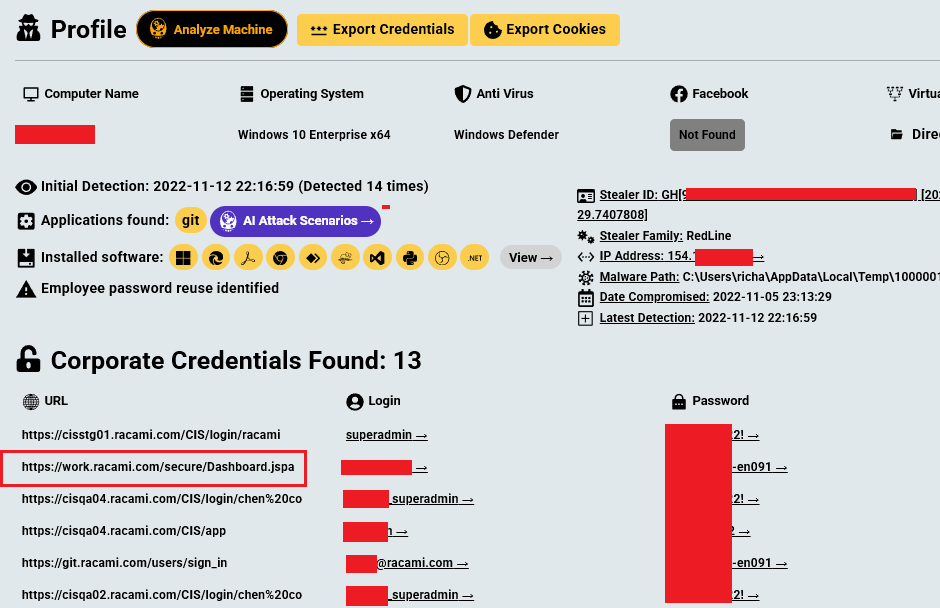
For these four latest breaches, Hudson Rock researchers investigated the compromised credentials using the company’s database. Below are the details of the Jira credentials identified for each organization, which HellCat likely used to gain initial access:
- HighWire Press, Inc (2022 Raccoon Infostealer log):
- Asseco Poland S.A. (2024 StealC Infostealer log):
- Racami, LLC (2022 Redline Infostealer log):
- LeoVegas Group (2024 Lumma Infostealer log):
These credentials were harvested by infostealers prior to the attacks, giving HellCat the keys to each organization’s Jira instance. From there, the group followed their usual modus operandi: exfiltrating sensitive data, posting proof of the breach on their leak site, and issuing ransom demands with a countdown timer.
The Fallout: What These Breaches Mean for the Victims
The impact of HellCat’s attacks on these four organizations is significant, both in terms of operational disruption and the potential for further harm:
- HighWire Press, Inc. serves scholarly publishers, meaning the stolen data could include sensitive research, intellectual property, or personal information of academics and researchers. A breach of this nature could undermine trust in the platform and lead to long-term reputational damage.
- Asseco Poland S.A. is a major IT solutions provider in Europe, with clients across industries like banking, healthcare, and government. The compromise of their internal systems could have a ripple effect, potentially exposing their clients’ data and disrupting critical services.
- Racami, LLC specializes in customer communications management, so the stolen data might include client communications, financial records, or proprietary software. This could lead to targeted phishing campaigns or intellectual property theft.
- LeoVegas Group, an online gaming and betting company, likely had customer data, financial transactions, and internal communications exposed. This puts customers at risk of identity theft and fraud, while the company faces regulatory scrutiny under laws like GDPR.
HellCat’s threats to leak or sell the stolen data add another layer of urgency. Even if the victims pay the ransom, a decision that rarely guarantees the safe return of data, the information could still end up on the dark web, fueling further attacks like phishing campaigns or business email compromise (BEC) schemes.
Why These Attacks Keep Happening and How to Stop Them
HellCat’s continued success highlights a critical gap in many organizations’ cybersecurity strategies: the failure to address infostealer malware as a precursor to ransomware attacks. Hudson Rock researchers have consistently emphasized that infostealers are often the first step in a much larger attack chain. Once credentials are stolen, they can be weaponized against systems like Jira, which serve as a gateway to an organization’s most sensitive assets.
The good news is that these attacks are preventable with the right measures in place. Here are steps organizations can take to protect themselves:
- Monitor for Infostealer Infections: Deploy endpoint detection and response (EDR) tools to identify infostealer activity on employee devices. Hudson Rock’s solutions provide real-time alerts on stolen credentials, empowering organizations to act before attackers can exploit them.
- Reset Compromised Credentials Immediately: If an infostealer infection is detected, reset all potentially compromised credentials and monitor for unauthorized access attempts. In the case of these four breaches, the stolen Jira credentials sat unused for weeks or months, giving HellCat ample time to plan their attacks.
- Secure Jira Instances: Implement multi-factor authentication (MFA) on all Jira accounts and use network segmentation to limit lateral movement. Jira’s centrality in enterprise workflows makes it a high-value target, so it must be locked down accordingly.
- Educate Employees: Many infostealer infections start with phishing emails or malicious downloads. Regular training can help employees recognize these threats and avoid falling victim.
A Call to Action: Don’t Be the Next Victim
HellCat’s latest attacks on HighWire Press, Asseco Poland, Racami, and LeoVegas Group serve as a stark reminder of the growing threat posed by infostealer malware and the ransomware groups that exploit it. As long as organizations fail to address this vulnerability, HellCat and other groups like them will continue to find new victims.
Hudson Rock remains committed to staying one step ahead of these threat actors. By identifying the compromised Jira credentials used in these attacks, Hudson Rock researchers aim to shed light on the tactics of groups like HellCat and help organizations better protect themselves.
Organizations should not wait until their name appears on a ransomware leak site. Investing in infostealer monitoring, securing critical systems, and taking proactive steps to mitigate this threat are essential. The next HellCat victim could be any organization, but with the right defenses, it does not have to be yours.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock