American cybersecurity company KnowBe4 says a person it recently hired as a Principal Software Engineer turned out to be a North Korean state actor who attempted to install information-stealing on its devices.
The firm detected and stopped the malicious actions in time, so no data breach occurred. However, the case highlights the continued threat posed by North Korean threat actors posing as IT staff, something that the FBI has warned about repeatedly since 2023.
The DPRK maintains a highly organized army of IT workers who obscure their true identities to get hired by hundreds of American firms.
Revenue generated by these workers are used to fund the country’s weapons programs and cyber operations, as well as to collect intelligence.
AI-assisted masking
Before hiring the threat actor, KnowBe4 performed background checks, verified the provided references, and conducted four video interviews to ensure they were a real person and that his face matched the one on his CV.
However, it was later determined that the person had submitted a U.S. person’s stolen identity to dodge the preliminary checks, and also used AI tools to create a profile picture and match that face during the video conference calls.
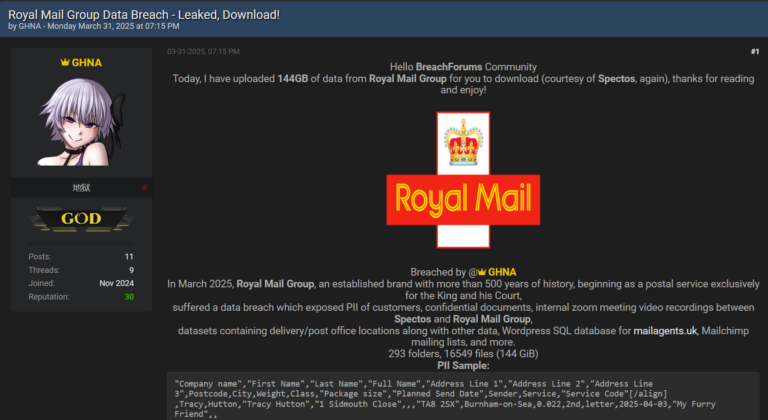
KnowBe4, which specializes in security awareness training and phishing simulations, suspected something was off on July 15, 2024, when its EDR product reported an attemp to load malware from the Mac workstation that had just been sent to the new hire.
A KnowBe4 spokesperson told BleepingComputer the malware was an infostealer targeting data stored on web browsers, and that the rogue employee was likely hoping to extract information left on the computer before it was commissioned to him.
“The attacker may [have used] this to find any credentials left over from previous browser sessions as a result of an IT department’s initial provisioning process or to extract information leftover from an incomplete or improperly wiped laptop previously issued to a different employee.” the KnowBe4 spokesperson told BleepingComputer.
When confronted by the firm’s IT staff about the activity, the state actor initially projected excuses but soon stopped all communication.
“When these alerts came in KnowBe4’s SOC team reached out to the user to inquire about the anomalous activity and possible cause. XXXX (the threat actor) responded to SOC that he was following steps on his router guide to troubleshoot a speed issue and that it may have caused a compromise.
The attacker performed various actions to manipulate session history files, transfer potentially harmful files, and execute unauthorized software. He used a Raspberry Pi to download the malware. SOC attempted to get more details from XXXX including getting him on a call. XXXX stated he was unavailable for a call and later became unresponsive.” KnowBe4
A post by KnowBe4 CEO Stu Sjouwerman explains that the scheme involves tricking the employer into sending the workstation to an “IT mule laptop farm” based near the location the fraudster declared as their home address on their application.
Then they use VPN to connect to that device during the nighttime, so it appears as if they’re working U.S. times, and perform the tasks given to them as normal.
To mitigate this risk, KnowBe4 suggests that firms maintain a sandbox for new hires isolated from their most critical network parts.
The company also says to ensure that new hire’s external devices aren’t used remotely and treat shipping address inconsistencies as a red flag.