By [Alon Gal] | April 2025
Just days after reporting on the Samsung Tickets data breach, another massive leak has surfaced, this time targeting Royal Mail Group, a British institution with over 500 years of history.
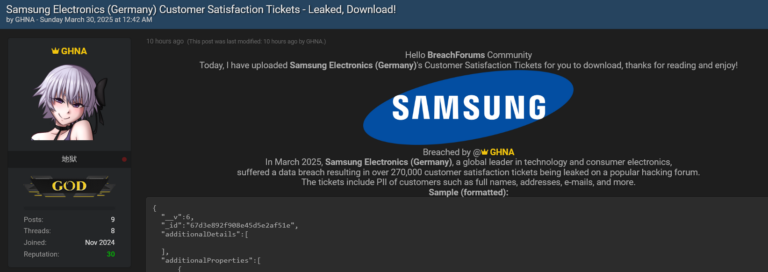
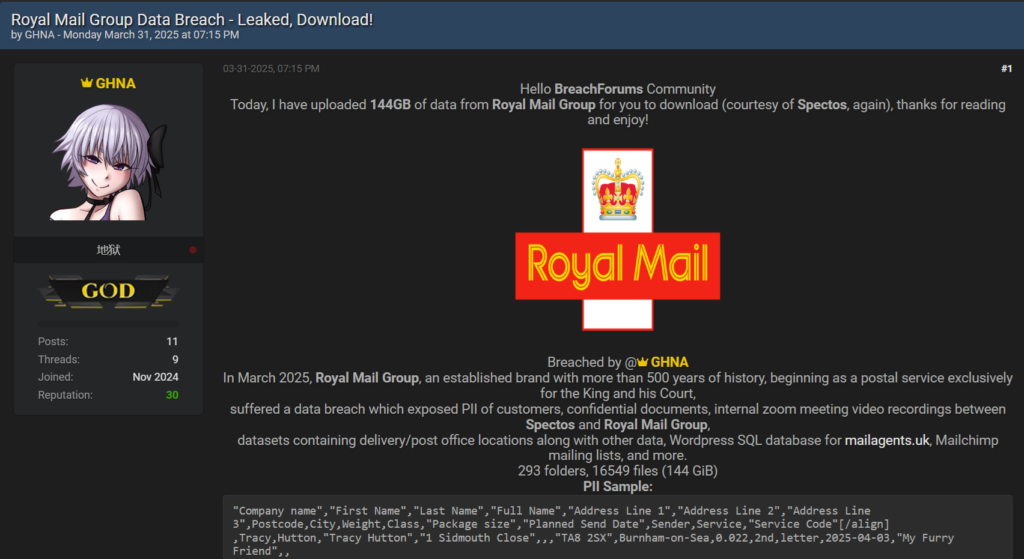
On April 2, 2025, a threat actor known as “GHNA” posted on BreachForums, announcing the release of 144GB of data stolen from Royal Mail Group. The breach, once again facilitated through Spectos, a third-party service provider, exposes personally identifiable information (PII) of customers, confidential documents, internal Zoom meeting video recordings, delivery location datasets, a WordPress SQL database for mailagents.uk, Mailchimp mailing lists, and more.
Hudson Rock’s investigation has traced this incident back to the same root cause as the Samsung breach: a 2021 Infostealer infection of a Spectos employee. Beyond the breach itself, the sheer volume of data highlights a growing trend: artificial intelligence (AI) is transforming these leaks into goldmines for hackers, a phenomenon equally applicable here.
The Breach Details
The leaked data, comprising 293 folders and 16,549 files, was made freely available for download on BreachForums. The threat actor’s post included a sample of the exposed PII, revealing fields such as full names, addresses, package details, and planned send dates. Here’s a snippet of the PII sample:
- Tracy ********, “1 Sidmouth Close, TA8 2SX, Burnham-on-Sea”, 0.022kg, 2nd class letter, Sender: “My Furry Friend”
- Peter ******, “1 Eskdale Close, Formby, L37 2YR, Liverpool”, 0.022kg, 2nd class letter, Sender: “My Furry Friend”
- Abdul ****-****, “Flat 8, Salford House, Seyssel Street, E14 3HZ, London”, 0.022kg, 2nd class letter, Sender: “The Color Co Ltd”
Additionally, a Mailchimp mailing list sample was included, exposing detailed subscriber information such as email addresses, phone numbers, physical addresses, and campaign-specific metadata. One entry highlighted:
- Gill *******, “gill.*******@gmail.com”, “27 Kenilworth Gardens, Loughton, IG10 3AF”, Phone: “+447979099***”, tagged with campaigns like “Private Campaign for MFM Feb 2025” and “Parcel Collect Survey.”
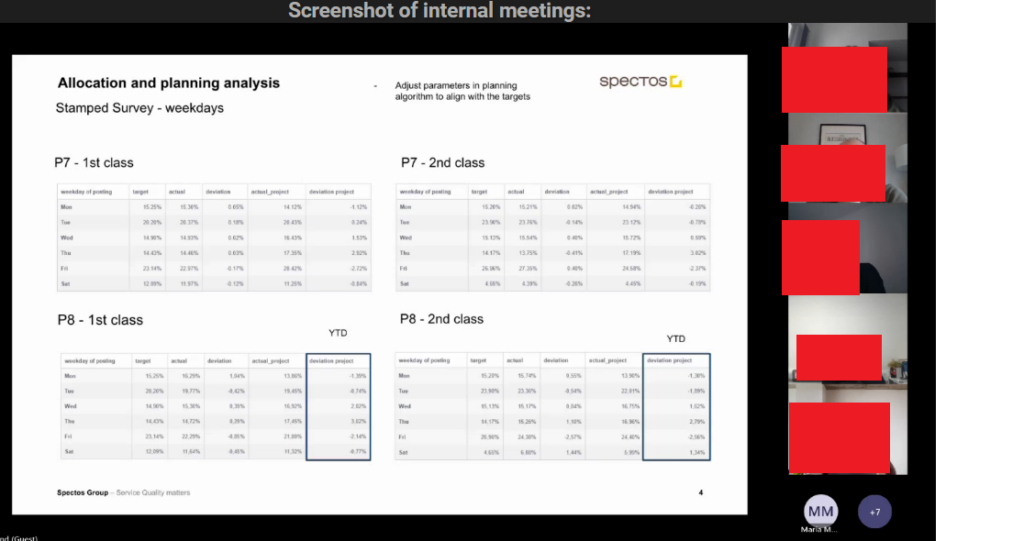
The dataset also contains internal Zoom recordings between Spectos and Royal Mail Group, delivery and post office location data, and a full WordPress SQL database for mailagents.uk, amplifying the breach’s impact.
Same Threat Actor, Same Weakness
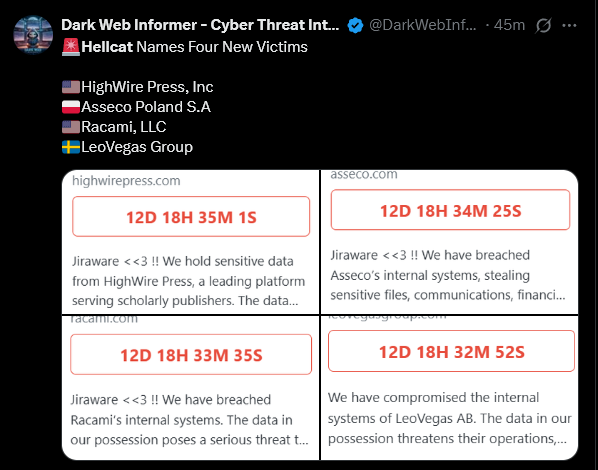
This breach bears striking similarities to the Samsung Tickets leak Hudson Rock covered earlier this week, both incidents involve the same threat actor, “GHNA,” and exploit vulnerabilities tied to Spectos, a company providing data collection and analytics services.
Hudson Rock’s analysis reveals that the root cause of both breaches is identical: a 2021 Infostealer infection that compromised the credentials of a Spectos employee.
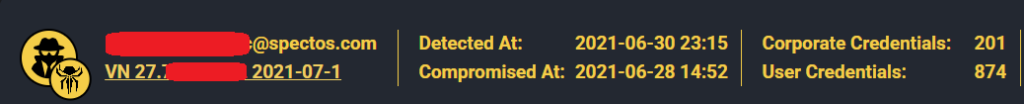
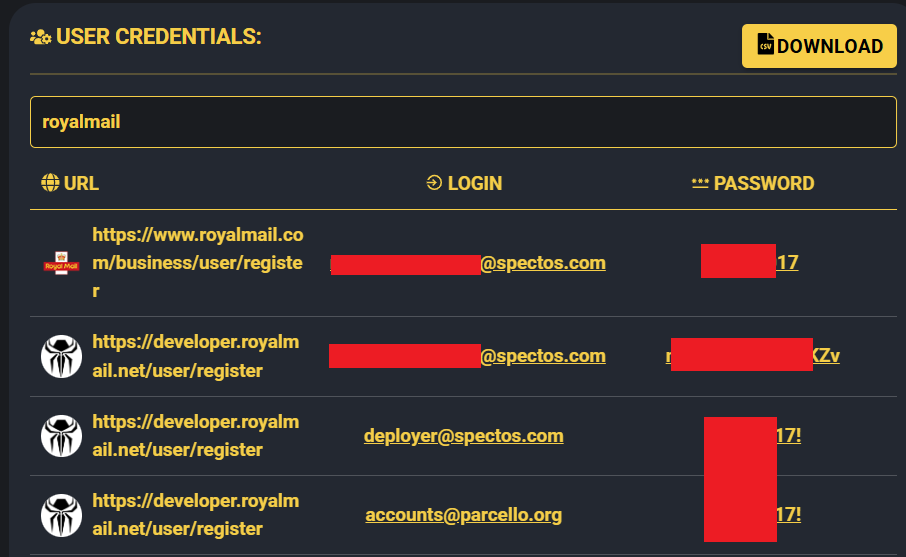
Infostealers, a type of malware designed to harvest credentials, browser data, and other sensitive information, have become a persistent threat to organizations relying on third-party vendors. In this case, the infected Spectos employee’s credentials provided a gateway to Royal Mail Group’s systems, much like they did for Samsung’s. The stolen data sat dormant until recently, when it was weaponized in these high-profile leaks.
AI’s Role in Amplifying the Damage
The scale of this breach, 144GB of unstructured data, mirrors the challenges seen in other recent leaks, such as the Orange incident I analyzed previously (see AI’s Role in Turning Massive Data Leaks into Hacker Paydays: A Look at the Orange Breach). What makes this leak particularly dangerous is not just its size, but how AI can transform it into a hacker’s payday. Tools like ChatGPT and custom-built AI models can rapidly parse through the 16,549 files, extracting valuable insights from PII, mailing lists, and internal documents. For instance, AI could identify high-value targets within the Mailchimp data, such as individuals linked to specific campaigns, or cross-reference delivery addresses with public records to build detailed victim profiles.
Moreover, the Zoom recordings and operational datasets offer a treasure trove for social engineering. AI-driven analysis could transcribe and summarize these videos, pinpointing key personnel or operational weaknesses at Royal Mail Group. This capability turns a raw data dump into actionable intelligence, enabling attackers to craft precise phishing campaigns or sell curated datasets on the dark web at a premium. As we noted in the Orange breach analysis, the speed and scalability of AI mean that what once took weeks of manual effort can now be accomplished in hours, exponentially increasing the breach’s fallout.
The Broader Implications
The Royal Mail Group breach underscores the cascading risks of supply chain attacks. With 144GB of data now in the wild, including customer PII, internal communications, and operational datasets, the fallout could include identity theft, phishing campaigns, and reputational damage. The exposure of Mailchimp mailing lists further amplifies the threat, as attackers can leverage AI to refine this information for targeted social engineering attacks.
This incident also highlights a critical lesson: credentials stolen years ago can remain valuable long after the initial infection. Organizations must prioritize continuous monitoring, robust third-party risk management, and proactive credential rotation to mitigate such risks. Additionally, the integration of AI into the hacker toolkit demands a shift in defensive strategies, with companies needing to anticipate how adversaries will exploit these tools against large-scale leaks.
Conclusion
The Royal Mail Group data leak, like the Samsung breach before it, is a stark reminder of the enduring danger posed by Infostealers. Hudson Rock’s tracing of both incidents to a single 2021 infection of a Spectos employee reveals a troubling pattern, one that organizations can no longer afford to ignore. Compounding this threat is the rise of AI, which turns massive data dumps into precision weapons for cybercriminals. As threat actors continue to exploit these vulnerabilities and technologies, the need for heightened cybersecurity vigilance has never been more urgent.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock