
PONY | FAREIT. Stealer, Loader, and Botnet.
_OVERVIEW Pony (also known as Fareit or Siplog) is a malware categorized as a loader and stealer, although it is also used as a botnet,

_OVERVIEW Pony (also known as Fareit or Siplog) is a malware categorized as a loader and stealer, although it is also used as a botnet,

Edit 03/02/24 – ‘Tamagami’ reveals they also possess access to Kodex which enables EDR / Subpoena requests for services such as LinkedIn, Discord, Tinder, Binance,

Malware is constantly evolving to become more evasive, destructive, efficient, and infectious. There are numerous families of malware, each with its own unique characteristics. These

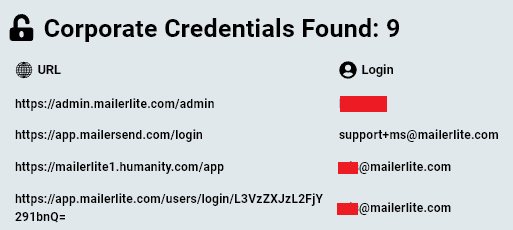
Following a recent and highly disruptive cyberattack on telecom carrier Orange España the cybersecurity community needs to rethink its approach to safeguarding the digital identity

In this Help Net Security interview, Alon Gal, CTO at Hudson Rock, discusses integrating cybercrime intelligence into existing security infrastructures. Our discussion will cover a range

Affected platforms: All platforms where PyPI packages can be installedImpacted parties: Any individuals or institutions that have these malicious packages installedImpact: Leak of credentials, sensitive information, etc.Severity level: High
The rise of infostealer malware has become a serious challenge for organizations worldwide. These sophisticated malware types are designed to stealthily infiltrate systems, extract sensitive
In ongoing efforts to monitor and analyze emerging cyber threats, Morphisec Threat Labs has recently turned its focus to Chae$ 4.1, an update to the
Cryptocurrency on-chain sleuth, ZachXBT, alerted the cryptocurrency community today that several notable organizations such as CoinTelegraph and WalletConnect are being used to send phishing messages

A month ago, we discovered some cracked apps circulating on pirating websites and infected with a Trojan proxy. The malicious actors repackaged pre-cracked applications as PKG files
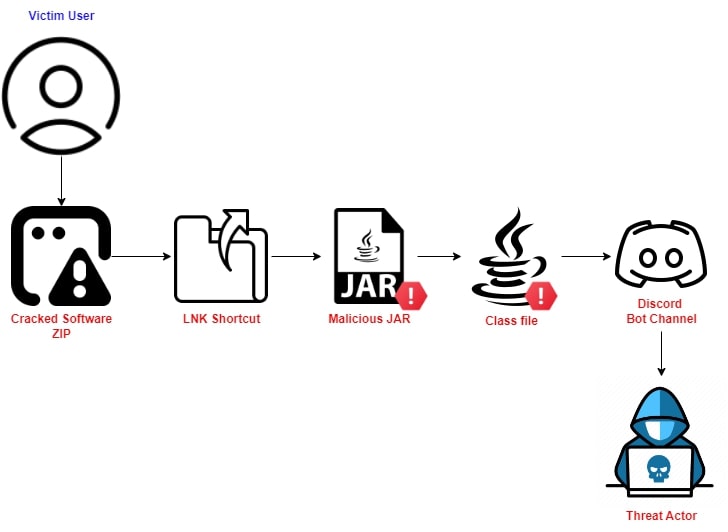
Executive Summary: In mid-November 2023, Trellix Advanced Research Center team members observed a Java-based stealer being spread through cracked software zip files using JDABuilder Classes

We have been reporting on the rise of infostealers targeting macOS since early last year, but threat actors show no signs of slowing down. Throughout

Executive Summary Overview The cloud hacktool scene is highly intertwined, with many tools relying on one another’s code. This is particularly true for malware families

Last year, we documented malware distribution campaigns both via malvertising and compromised sites delivering Atomic Stealer (AMOS) onto Mac users. This stealer has proven to be quite popular in
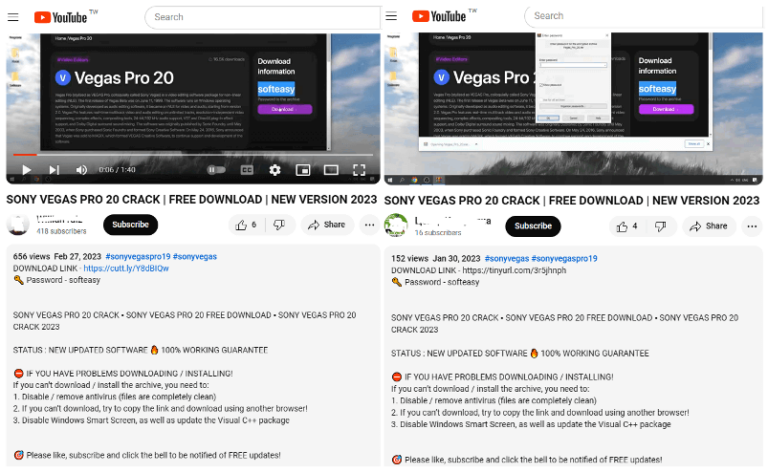
FortiGuard Labs recently discovered a threat group using YouTube channels to distribute a Lumma Stealer variant…

To completely understand what’s going on in the info stealers market which has been growing in the last years…
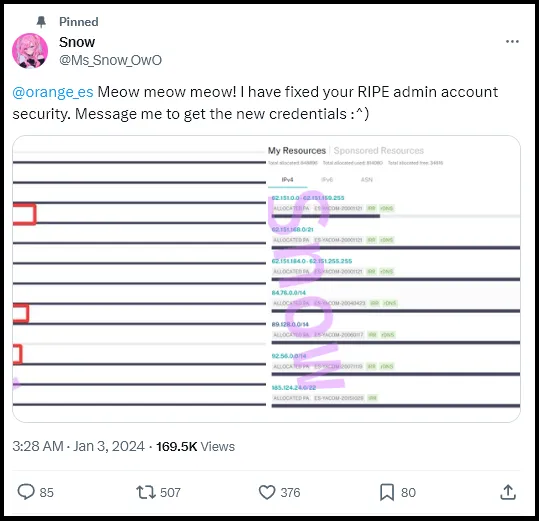
Using the stolen account, the threat actor modified the AS number belonging to Orange’s IP address, resulting in major disruptions…
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…
Stay informed with the latest insights in our Infostealers weekly report. Explore key findings, trends and data on info-stealing activities.
