
Botnets & Info-Stealers (Part Ⅲ)
In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…
Home » Cyrus

In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…

In this second of a three blog post series, Cyrus and Hudson Rock reveal how the info-stealer threat looks from the hacker’s point of view…

An information stealer is a type of malware that gathers sensitive information stored on a device. Once a computer has been infected, the info-stealer uses various techniques to acquire data…
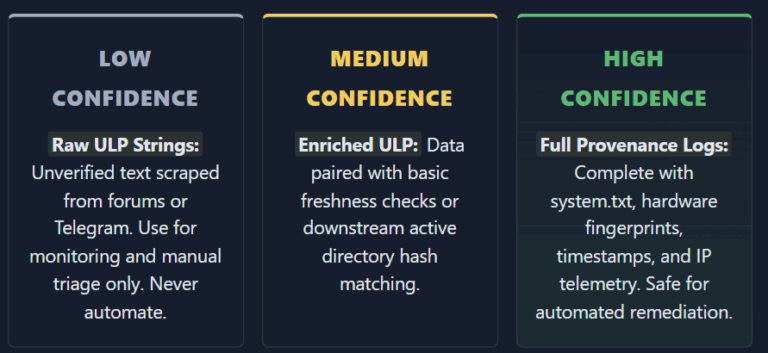
Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation The cybersecurity industry
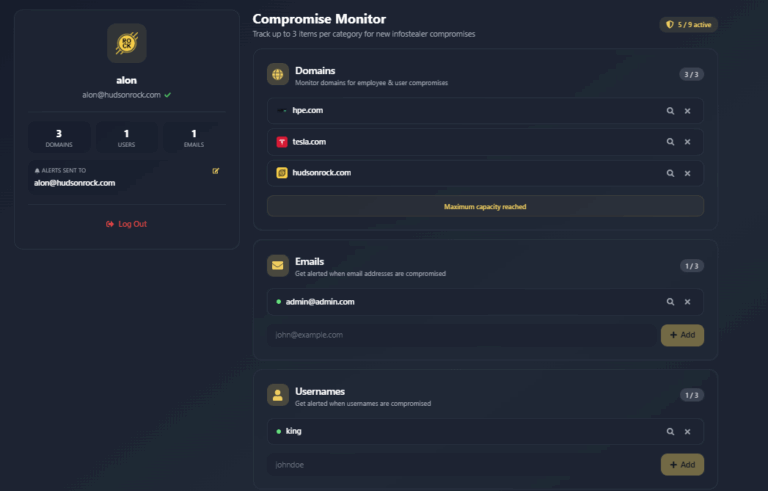
Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3 Usernames Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3
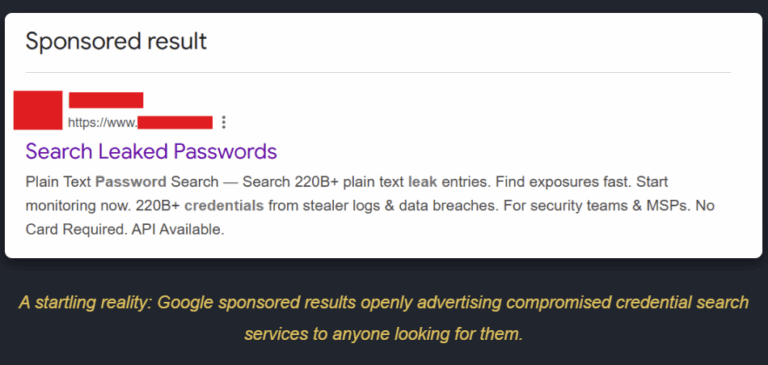
The New Era of Initial Access: How Infostealer Lookup Services are Changing Cybercrime We are currently witnessing a massive shift in how cyberattacks begin. Infostealer
